Executive Summary
zLabs researchers have been tracking a Necro.N, a mobile malware campaign, since July. Expanding upon Kaspersky’s report, we’ve gathered additional insights. Over this time, we’ve collected more than 30 samples and few of them had low detections from other security vendors.
As stated in the original report, Necro.N is highly intrusive and is emerging as a significant threat, positioning it as a potential successor of the notorious malware Joker. This analysis of Necro.N will focus on the differences and elements not reported by the original research. For a comprehensive overview of the functioning of this malware, readers should refer to the original blog.
Extending the Discovery
The reported version for the malware uses obfuscation techniques to evade detection and hinder analysis. Additionally, it utilizes steganography to hide the malicious payloads within images. The malware downloads the payload from a C2 server (Command & Control Server), allowing it to execute remote code on the infected device. This malicious code can perform actions such as installing applications, opening links in invisible WebViews to execute JavaScript code and subscribing victims to unwanted paid services, functioning as a “fleeceware” threat.
Threat actors crafted a deceptive advertising SDK that promised substantial rewards to its users. This SDK was designed to be integrated into mobile applications, attracting developers with the prospect of increased revenue. However, these developers were unaware the SDK contained malicious code and was secretly distributed to unsuspecting users through the apps that incorporated it. The core element of the malware is a native library called “libcoral.so”. After the initialization, this library establishes contact with the C2 server to retrieve the payload’s location.

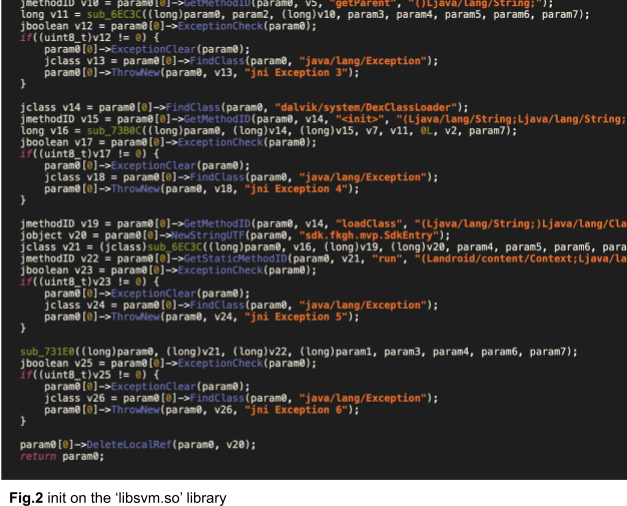
The library leverages a steganographic algorithm to decode the hidden payload within the image. Once extracted, the code is loaded and executed on the device. Zimperium researchers discovered another library, “libsvm.so”, that functions similarly and is employed in multiple malware samples.
The C2’s response indicates this is a recent version of the SDK, as evidenced by the “sdkver” field reporting a value of 101. Suggesting the threat actor remains active and continues to develop and refine the malware. Despite the release of a new SDK version, the domain used to distribute the first stage payload remains unchanged and is still active.
A Numerical Breakdown
Our monitoring efforts yielded a total of 37 malware samples.
Here’s a breakdown of the distribution:
- libcoral.so: 29 samples (78%) were identified to utilize this library for its malicious functionalities.
- libsvm.so: a smaller subset of 8 samples (22%) employed the alternative library. These samples exhibited low or even zero detection rates from other vendors.
Delving deeper, we discovered variations within both libraries:
- libsvm.so: we identified 2 distinct hashes for the ‘libsvm.so‘ library.
- libcoral.so: a wider range of variations was observed with the ‘libcoral.so‘ library, with 12 unique hashes discovered.
This breakdown provides a clear picture of the malware’s composition and highlights the potential challenges posed by the evasive nature of the ‘libsvm.so’ library.
Zimperium vs Necro.N
Given the malware’s capabilities, to safeguard enterprise users and devices from this malware and others similar, it is critical to deploy proactive, robust protection and mitigation measures to prevent data or financial loss.
Zimperium is uniquely equipped to support enterprises (MTD) and app developers (MAPS) in defending against the constantly evolving threat landscape targeting mobile devices. Powered by our proprietary On-Device Dynamic Detection Engine, both MTD and MAPS products leverage local, on-device advanced machine learning, behavioral analysis and deterministic detection, to deliver comprehensive threat detection and mitigation without compromising user experience or development timelines.
Our cutting-edge detection engine has successfully identified and neutralized all malware samples and malicious URLs discussed in this blog post, underscoring its unmatched effectiveness in protecting against emerging cyber threats.
MITRE ATT&CK Techniques
| Tactic | ID | Name | Description |
| Initial Access | T1661 | Application Versioning | Distributed through official app stores and integrated into applications by unaware developers. |
| Execution | T1575 | Native API | Samples initialize the malicious code using native calls. |
| Persistence | T1398 | Boot or Logon Initialization Scripts | Able to execute the app once the device boot is done. |
| T1624.001 | Event Triggered Execution: Broadcast Receivers | Able to register the app via BOOT_COMPLETE receiver. | |
| Defense Evasion | T1407 | Download New Code at Runtime | Sample downloads a dex file at Runtime and loads the code at runtime. |
| T1406.001 | Obfuscated Files or Information: Steganography | Samples use Steganography to hide the DEX payload inside an image file. | |
| T1406.002 | Obfuscated Files or Information: Software Packing | Malware is using code obfuscation techniques. | |
| Credential Access | T1517 | Access Notifications | Few samples are able to access the device notifications. |
| Discovery | T1426 | System Information Discovery | Samples extract device info like IMEI, operating system info, etc, and exfiltrate it to the server. |
| Collection | T1517 | Access Notifications | A few samples can access the device notifications. |
| Command and Control | T1437.001 | Application Layer Protocol: Web Protocols | Malware uses HTTP protocol to communicate with the C2. |
Indicators of Compromise (IOCs)
Hashes can be found here.


